
Vulnerability Assessment and Penetration Testing
Cybersecurity Penetration Testing for Continuous Risk Validation
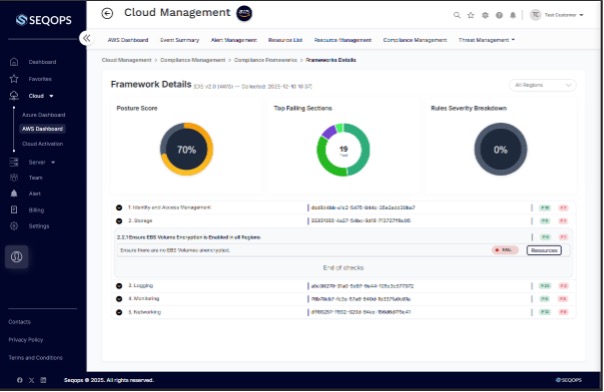
SeqOps enables vulnerability assessment and penetration testing as a continuous, product-led capability to help teams identify exposure and validate defenses against real-world attack paths. This approach strengthens cybersecurity penetration testing by maintaining ongoing visibility into risk and overall risk visibility without relying on manual or expert-driven testing models.
Vulnerability Assessment and Penetration Testing at Scale
In today’s complicated security world, it’s important to always be aware of risk. SeqOps is an automated, product-led platform that helps teams find weaknesses early and lower their risk before problems get worse. It does this by allowing vulnerability assessments and penetration testing.
SeqOps goes beyond periodic checks by supporting ongoing continuous security validation workflows. It is built on a continuous model. As environments change, this approach helps businesses stay aware of attack paths and exposure points.
Designed for Scalable Security Operations
SeqOps integrates automated testing and analysis directly into security workflows, helping teams track findings, prioritize risk, and maintain consistency without relying on manual or expert-driven processes.
Reduce Effort While Strengthening Defense
SeqOps helps lower operational costs and improve security over time by centralising testing results and making them easier to see. This lets teams focus on making systems more resilient and safe in the long term.
Go Beyond Periodic Tests with Pentest Testing
Instead of one-time checks, modern security requires continuous visibility. SeqOps enables automated penetration testing on a platform that continuously evaluates system security and highlights new risks as environments change.
SeqOps works all the time to find weaknesses early, instead of relying on scheduled or manual testing cycles. This method helps companies cut down on the time they are exposed and keep their defences strong without relying on security models that are based on services.
SeqOps helps with a structured testing lifecycle that aligns security improvement with business priorities by centralising findings and keeping an eye on risk over time. As threats change, teams get a clearer picture, less operational friction, and more consistent protection.
Vulnerability Assessment Penetration Testing with SeqOps
Add Your Assets
Securely connect your environment to begin vulnerability assessment penetration testing. SeqOps starts automated discovery to build visibility into exposure points without manual setup.
Prioritize What Matters
Findings are analyzed through continuous security validation logic to highlight risks based on impact, helping teams focus remediation where it matters most.
Monitor Continuously
SeqOps runs continuously to surface changes and emerging risks, supporting ongoing visibility and consistent overall risk visibility as environments evolve.
Cybersecurity Penetration Testing
SeqOps offers a proactive, product-led approach to cybersecurity penetration testing that helps businesses stay one step ahead of new threats while keeping important data and systems safe. Automated analysis and continuous visibility help make security stronger without having to do periodic or manual testing.
SeqOps enables teams to understand exposure, validate defenses, and maintain confidence as environments change using a scalable platform built for continuous security improvement.

Why Choose SeqOps for Continuous Penetration Testing Cybersecurity
Improved Security Testing Outcomes
SeqOps strengthens overall risk visibility through continuous security validation that continuously validates defenses and highlights exploitable paths as environments change.
Scalable Penetration Testing Cybersecurity
Built for growth, SeqOps supports continuous security validation by adapting testing coverage as infrastructure expands, without added operational complexity.
Flexible Testing Configuration
SeqOps enables continuous penetration testing with configurable scopes, allowing teams to align testing depth and frequency with evolving risk requirements.
Continuous Cybersecurity Penetration Testing
The platform delivers ongoing cybersecurity penetration testing to surface weaknesses early and reduce exposure between traditional testing cycles.
Clear Vulnerability Comparison Insights
SeqOps helps teams understand risk by clearly distinguishing penetration testing vs vulnerability scanning, supporting better prioritization and decision-making.
Actionable Assessment Clarity
By combining discovery and validation, SeqOps supports vulnerability assessment vs penetration testing to give teams clearer insight into real-world security impact.
Six Easy Steps To A Safer Business With SeqOps Penetration Testing
Connect Your Environment
SeqOps securely connects your environment to start automated discovery. This step initiates penetration testing assessment by mapping assets, services, and access paths to establish baseline visibility.
Define Testing Scope
Discovered assets are analyzed to determine testing coverage based on configuration, exposure level, and potential attack surfaces across the environment.
Apply Contextual Inputs
Configuration data, behavior signals, and system context are used to ensure testing reflects real-world conditions and realistic attack scenarios.
Execute Continuous Testing
SeqOps continuously evaluates systems to uncover exploitable weaknesses, validate controls, and identify security gaps as changes occur.
Review Clear Findings
Findings are presented in a clear, structured format that helps teams understand impact, severity, and trends without unnecessary complexity.
Strengthen Defenses Over Time
Ongoing visibility allows teams to track improvements, reduce exposure, and maintain stronger protection maturity.
Continuous Vulnerability Penetration Testing for Proactive Cyber Resilience
SeqOps lets teams do vulnerability penetration testing all the time, based on the product, so they don’t have to do it only once in a while. This way, they can always be aware of security holes as systems and configurations change.
SeqOps doesn’t use static testing cycles; instead, it runs all the time to check for exposure and find new risks in almost real time. This method uses ethical hacking penetration testing principles to find weaknesses that traditional testing models often miss by using automated validation, shorter detection windows, and surfacing weaknesses.
SeqOps helps make systems more resistant to cyber attacks by adding continuous validation to daily security tasks. Teams can see risk trends and attack paths more clearly, which helps them protect important assets and adapt confidently as the threat landscape changes.
Top Three Reasons for Choosing SeqOps
SeqOps stands out because it offers continuous security validation through an automated platform. SeqOps supports attack path validation workflows that help teams maintain overall risk visibility in real time, instead of relying on manual or periodic checks.
Product-Led Security Model: SeqOps operates as a scalable platform that integrates assessment and validation into ongoing security workflows, reducing reliance on manual processes and fragmented tools.
Built for Long-Term Resilience: Continuous evaluation helps organizations stay prepared as environments and threats evolve, supporting stronger defenses without disrupting day-to-day operations.
Always-On Risk Awareness: By continuously tracking changes and exposure, SeqOps helps teams stay ahead of potential threats and make informed security decisions with confidence.
Pricing Plans for SeqOps Server Security
SeqOps doesn’t just protect; it empowers. Its comprehensive reporting transforms raw data into actionable insights, helping administrators:
Basic
Per month price:
30 Days
Scanning Frequency
What you get:
- Monthly reporting
- Vulnerability detection
Advanced
Per month price:
30 Days
Scanning Frequency
What you get:
- Monthly reporting
- Vulnerability detection
Enterprise
Custom Quote
Full security and tailored to your needs
30 Days
Scanning Frequency
What you get:
- Managed Detection
- GDPR and NIST Reporting
- Threat alerts and attempt block
- Daily scans and reporting
Related Posts
- /
Data breaches now cost businesses an average of $4.45 million per incident, a record high according to the...
- /
Did you know that over 60% of data breaches result from unpatched security flaws that organizations knew about...
- /
A staggering 68% of businesses experience a significant security incident within their first year of operation. This alarming...
Frequently Asked Questions
What is continuous penetration testing?
Continuous penetration testing is a way to keep checking security that checks defenses as environments change. Cybersecurity penetration testing doesn’t just look at attack paths and system behavior once; it does it all the time. This helps teams stay aware of real-world risks as configurations, users, and assets change.
What are the benefits of continuous penetration testing?
The primary benefit is reduced exposure time. Continuous penetration testing helps identify exploitable weaknesses early, rather than weeks or months after changes occur. This continuous visibility supports better prioritization and more confident security decisions.
How long does a penetration test take?
Traditional tests only run for a set amount of time, but pentest testing runs all the time. Testing automatically changes when new assets are added or configurations are changed. This makes sure that security validation is always up to date, even if you have to wait for the next scheduled test.
Why do I need penetration testing if I already do vulnerability scanning?
Vulnerability scanning identifies known issues, but it does not show how attackers might chain weaknesses together. The difference between scanning and testing is best explained through penetration testing vs vulnerability scanning, where testing focuses on validating real attack paths and actual risk.
Can penetration testing help validate real security risk?
Yes. Discovery and validation work together to help vulnerability assessment and penetration testing find the weaknesses that can actually be used. This helps teams focus their efforts on fixing problems that will have the biggest effect on the real world.
How is continuous penetration testing different from traditional assessments?
Traditional tests happen at set times and quickly become out of date. Vulnerability assessment vs penetration testing shows how continuous testing maintains overall risk visibility between assessments, adapting as environments change and providing ongoing insight into risk posture.
Ready to Improve How You Manage Security?
Discover how the SeqOps platform helps your business work more efficiently while keeping your organization secure now and as you grow.